MSc in Cyber Security
This Program is accredited by the MFHEA
Cyber Security Course Overview
The MSc in Cyber Security is designed for graduate engineers aspiring to advance into cyber security management careers within technological organizations. In a global economy, it is vital for companies to hire and develop new talent that can bridge communication gaps in many contexts.
Our students are trained to understand computer and network technologies, and how to secure and protect their operations as well as the applications and data. In a global context, our students are adept at finding common ground and fostering international ties to create new ideas and perspectives. Our program focuses on creating leaders who are able to adapt to exploit emerging cyber technologies and have the knowledge and expertise to secure and manage their operations against cyber attacks.
Entry Requirements for this Program
Students are expected to have undergraduate training in mathematics, physics, computing, and mathematical modeling. Specifically, all incoming students are expected to meet the following fundamental requirements: 1) four semesters of mathematics, beginning with a two-semester sequence in calculus, 2) three semesters of calculus-based physics and general engineering science, 3) one semester of computing (e.g., an introductory course using a high-level language such as Java, C++, C#, Visual Basic, C, or Python).
Most undergraduate programs in science and engineering provide the required background. Students deficient in one or a small number of these areas may be admitted into the MSc program on Provisional Status. During the first semester, students who are on Provisional Status will need to take courses to address the deficiencies. As soon as deficiencies are removed, students are advanced to the regular graduate status. In addition to the fundamental requirements, all students who enter the MS program must also demonstrate satisfactory understanding of Introduction to Probability and Statistics.
Admission is based on evaluation of the applicant's letter of intent, undergraduate transcript, IELTS or TOEFL score, letters of recommendation, and professional experience. Applicants are expected to have an undergraduate GPA of 3.00 on the last 60 units of course work, 79 TOEFL or 6.5 IELTS.
PROGRAM DETAILS
Program length:
24 Months.
GPA needed to earn the degree:
3.0 or higher
Credits needed to earn the degree:
45US credists / 96ECTS
Degree level:
MQF Level 7
Pass Rate:
80%
OVERALL COURSE OBJECTIVES
Students completing the program are expected to be able to apply the methodology and tools learned in this program to effectively secure and protect the operations of computer networks, computing systems, data and applications. Students are expected to learn equally cyber security fundamentals as well as hands on in effective use and deployment of current and emerging cyber security solutions and tools.
By completion of the MSc program in cyber security engineering, a student will: (a) Master the intricacies and vulnerabilities of computer networks, computing systems, clouds, and web applications; (b) Learn how to develop algorithms that detect, protect against, and minimize the effectiveness of cyber attacks that target networks, protocols, operating systems, computers and web applications. (c) Contribute to the development of the next generation of tools and solutions in the domain of cyber security engineering.
LEARNING OUTCOMES FOR CYBER SECURITY SKILLS OBTAINED AT THE END OF THE PROGRAM
The learner will be able to: (a) Acquire the skill set necessary for detecting cyber security threats and predicting their impact should they strike. (b) Develop secure and resilient mechanisms for the protection of computer networks and software. (c) Defend against cyber attacks when they occur, minimize their impact, and assess the damage done (d) Utilize effective current security tools and appliances to manage and secure the operations of cyber resources and their services. (e) Communicate the current security posture of the organization and develop a plan to identify vulnerabilities and how to address them.
General Pedagogical Methods used for this Program
The method of teaching follows the standard classroom model in which the primary mode of instruction is lectures, laboratory experiments, and engagement with students through discussion. The instructor provides material, including where appropriate videos, for the students to study outside of class. In class, in addition to lectures to clarify the material, the instructor leads in-class exercises (problems, design projects, instructing on software, discussions, etc). In addition, there will be lab experiments to enable students to comprehend the security fundamentals discussed in the class and acquire hands on in using and applying learned concepts to secure and protect computers, networks, data and applications. Out of class reading and homework assignments are regularly assigned, submitted and graded. Students also have the opportunity to engage in one-on-one instruction through office hours given by the course (module) instructor.
GENERAL ASSESSMENT POLICY AND PROCEDURES
Assessments Engineering disciplines require strong mathematics skills. Assessments (in-class examinations, homework and individual and team projects) will focus on those skills. In general, grades will be assigned based on performance on those assessments. Students with learning disabilities will be addressed. Additional time or quiet settings will be provided for examinations for those students as determined appropriate. Cheating and Plagiarism Exams will be administered in classroom settings by the instructor. Appropriate identification will be required. Class notes or limited sets of materials may be available to students during exams. Only simple calculators without memory cards will be permitted to avoid students bringing additional materials to assessments. The plagiarism tool, Turn-it-in, will be applied to document reports and papers are not copied from other sources without proper citation.
RELATIONSHIP TO OCCUPATION/S
The MSc cyber security degree program is intended to produce graduates who are able to develop and implement effective security solutions for computer networks, computing systems, data and applications. This Program is in response to student and employer demand for a highly skilled workforce in cyber security that knows the fundamentals of cyber security and how to utilize emerging security technologies and tools to secure and protect employer cyber infrastructures. This degree program does not lead to a warranted profession or regulated occupation.
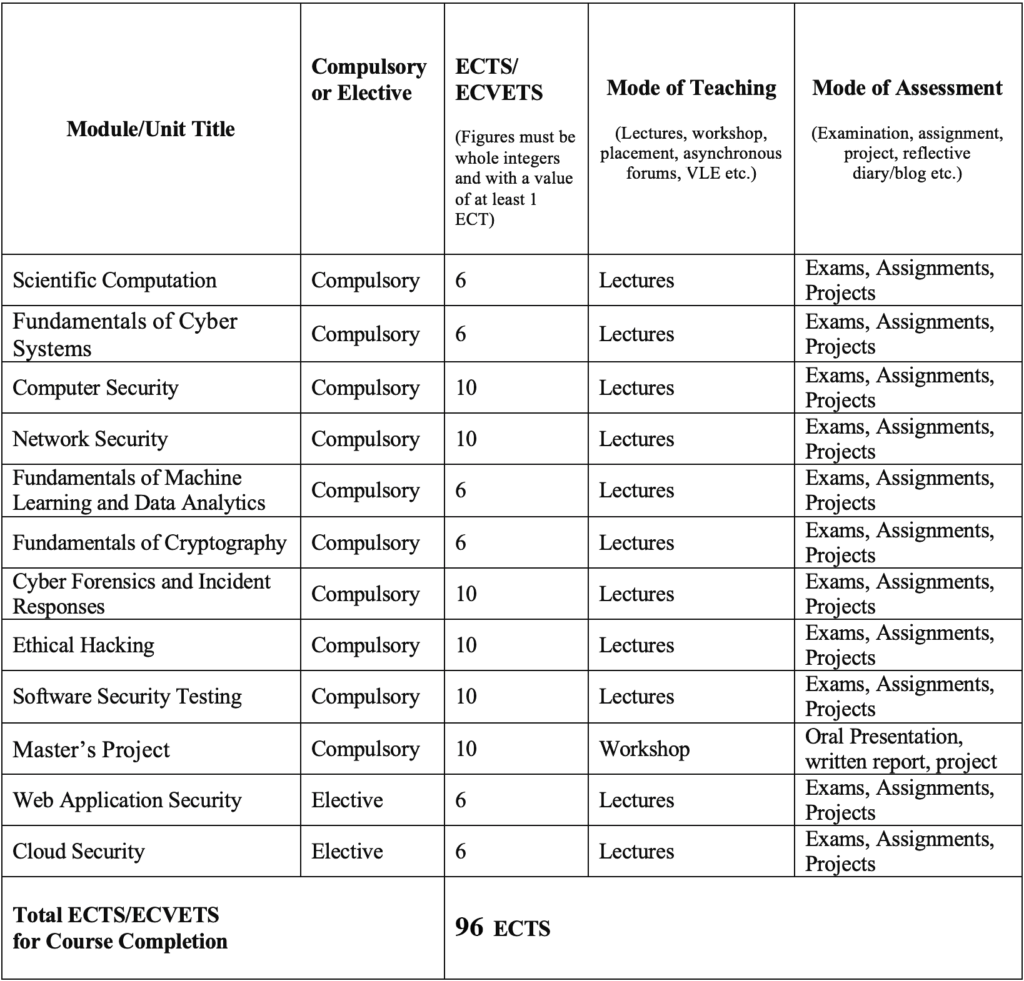
COURSE STRUCTURE SAMPLE